- Home
- Blog
- Smart Manufacturing
- Cybersecurity for Manufacturers: Protecting Your S…
Cybersecurity for Manufacturers: Protecting Your Shop Floor and Data
Cybersecurity in manufacturing has moved from an IT concern to an operational survival issue. As factories connect more machines, deploy more IoT sensors, and integrate more systems, the attack surface grows. Ransomware attacks on manufacturers increased over 70% between 2022 and 2025, and the average cost of a manufacturing cyberattack exceeds $2 million when accounting for downtime, recovery, and lost business. For any manufacturer pursuing smart manufacturing, cybersecurity is not optional — it is foundational.
Why Manufacturers Are Prime Targets
Valuable Intellectual Property
Product designs, manufacturing processes, customer specifications, and pricing data have significant value. Nation-state actors and competitors target this data for economic advantage.
Low Downtime Tolerance
Manufacturers cannot afford to stop production. This makes ransomware especially effective — the cost of a week's lost production often exceeds the ransom, creating a financial incentive to pay. Attackers know this.
Legacy OT Systems
Operational Technology (OT) — CNC controllers, PLCs, SCADA systems — was designed for reliability, not security. Many machines run decades-old operating systems (Windows XP, Windows 7) that no longer receive security patches. These systems cannot be easily upgraded without replacing expensive equipment.
Increasing Connectivity
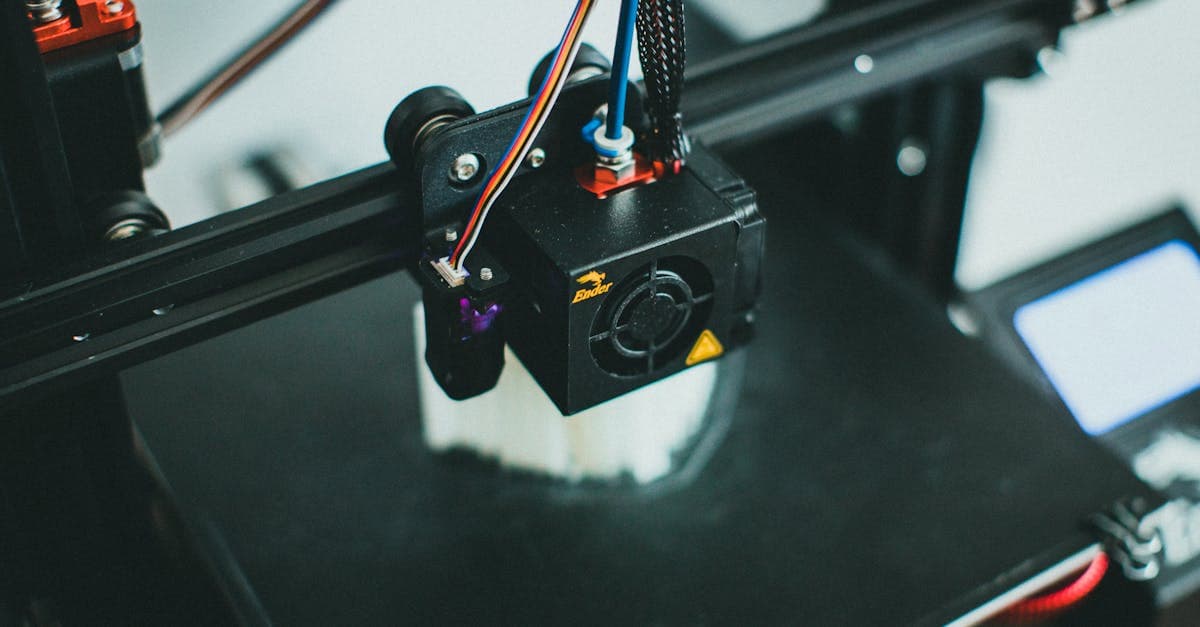
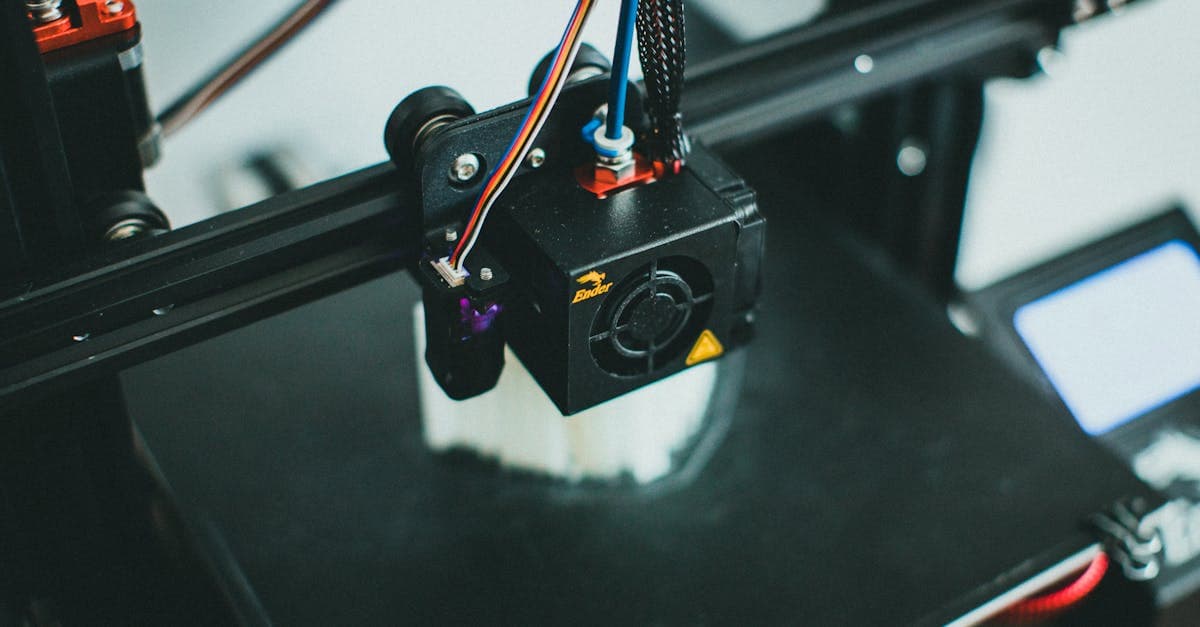
Industry 4.0 connects formerly isolated systems. IoT sensors, cloud software, remote access for vendors, and IT/OT convergence create network paths that did not exist when machines were standalone.
Supply Chain Pressure
Large OEMs increasingly require cybersecurity compliance from suppliers. A breach at a small supplier can compromise the entire supply chain — and large customers are mandating security standards accordingly.
Common Manufacturing Cyber Threats
Ransomware
Malware that encrypts your systems and demands payment for decryption keys. In manufacturing, ransomware can encrypt:
- ERP systems (blocking order management and financials)
- Scheduling systems (eliminating production planning visibility)
- CNC programs (disabling machine operation)
- Quality records (compromising compliance documentation)
Phishing and Social Engineering
Email-based attacks that trick employees into clicking malicious links or providing credentials. Phishing remains the most common initial entry point for manufacturing cyberattacks.
Insider Threats
Disgruntled employees, careless credential handling, and unauthorized access. A departing employee with administrative access to the MES or scheduling system can cause significant damage.
Supply Chain Attacks
Compromised software updates, infected vendor connections, or breached partner systems that provide lateral access to your network.
Industrial Espionage
Targeted attacks aimed at stealing proprietary manufacturing processes, designs, or customer data. Particularly relevant for defense, aerospace, and advanced technology manufacturers.
Practical Cybersecurity Steps for Manufacturers
Priority 1: Network Segmentation
Separate your IT network (email, ERP, internet access) from your OT network (machines, PLCs, IoT sensors). If an employee clicks a phishing link in email, the infection should not reach your CNC controllers.
- Use industrial firewalls between IT and OT zones
- Create DMZ (demilitarized zone) for systems that need both IT and OT access
- IoT gateways should bridge networks securely, not merge them
- Schedule regular reviews of network access rules
Priority 2: Backup and Recovery
If ransomware encrypts everything, your backups are your lifeline:
- Maintain offline (air-gapped) backups of critical systems
- Include scheduling data, ERP databases, CNC programs, and quality records
- Test recovery procedures quarterly — a backup you have never restored is not a backup
- Keep backup retention long enough to recover from delayed-discovery attacks (60-90 days minimum)
On-premise scheduling software like RMDB simplifies backup because your data is on your server, under your control. You determine the backup strategy, schedule, and recovery process.
Priority 3: Access Control
- Implement multi-factor authentication (MFA) on all internet-facing systems
- Use role-based access — operators do not need administrative access to scheduling or ERP
- Remove access immediately when employees leave
- Audit access rights quarterly
- Use unique accounts — never share credentials between users
Priority 4: Patch Management
- Patch IT systems (Windows, email, ERP) within 30 days of security updates
- For OT systems that cannot be patched (legacy CNC controllers), compensate with network segmentation and monitoring
- Maintain an inventory of all connected systems and their patch status
Priority 5: Employee Training
- Regular phishing awareness training (quarterly minimum)
- Teach operators to recognize suspicious USB devices, unusual machine behavior, and social engineering
- Create a culture where reporting suspicious activity is encouraged, not punished
- Conduct simulated phishing tests to measure and improve awareness
CMMC and Defense Manufacturing
The Cybersecurity Maturity Model Certification (CMMC) is a DoD requirement that affects all manufacturers in the defense supply chain:
CMMC Levels
- Level 1: Basic cyber hygiene — 15 practices (most small suppliers)
- Level 2: Advanced — aligned with NIST SP 800-171, 110 practices
- Level 3: Expert — for highest-sensitivity programs
Impact on Manufacturers
Defense manufacturers must achieve the required CMMC level to bid on DoD contracts. Even if you are a Tier 3 or Tier 4 supplier, if Controlled Unclassified Information (CUI) flows through your systems, CMMC applies.
Scheduling and CMMC
Production schedules for defense work may contain CUI — delivery dates, quantities, and capacity allocation for defense contracts reveal program details. Keeping scheduling data on-premise using tools like RMDB rather than in third-party clouds simplifies CMMC compliance for the scheduling function.
Cybersecurity and Smart Manufacturing Investment
Cybersecurity should be part of every smart manufacturing investment, not an afterthought:
IoT Security
- Change default passwords on all IoT devices before deployment
- Use encrypted communication between sensors and gateways
- Keep IoT firmware updated
- Segment IoT devices on dedicated network VLANs
Cloud Security
- Evaluate cloud vendors' security certifications (SOC 2, ISO 27001)
- Understand data residency — where your data physically lives
- Review vendor access policies — who can see your data?
- Ensure contractual protections for data handling and breach notification
- See our cloud vs on-premise analysis for deployment decisions
Automation Security
- Secure robot and cobot network connections
- Protect programming interfaces from unauthorized access
- Include automated systems in vulnerability assessments
Frequently Asked Questions
Manufacturers are attractive targets because they have valuable intellectual property (designs, processes), operational technology that is often poorly secured, low tolerance for downtime (making ransomware especially effective), and increasing connectivity between IT and OT systems that creates new attack surfaces.
Ransomware is currently the biggest threat. Attackers encrypt production systems and demand payment to restore access. Manufacturing is disproportionately targeted because the cost of downtime often exceeds the ransom, making victims more likely to pay. Phishing emails are the most common entry point.
CMMC (Cybersecurity Maturity Model Certification) is a DoD requirement for defense contractors. Manufacturers in the defense supply chain must achieve CMMC certification to bid on DoD contracts. Even non-defense manufacturers benefit from CMMC frameworks as a cybersecurity roadmap.
IoT devices connected to the shop floor create new network entry points. Many IoT sensors have limited built-in security, use default passwords, and run outdated firmware. Without proper network segmentation, a compromised IoT sensor can provide access to production systems and business networks.
On-premise scheduling software like RMDB reduces attack surface by keeping production scheduling data off the internet. It eliminates third-party cloud access to operationally sensitive data (schedules, customer priorities, capacity information) and ensures scheduling operates independently of internet-dependent systems.
Keep Your Scheduling Data Secure
RMDB runs on-premise, keeping your production scheduling data under your control. No cloud dependency, no third-party access to your schedules, no internet requirement for daily operation. For defense manufacturers, this simplifies CMMC compliance. For everyone, it means security you can trust. Contact User Solutions to learn more.
Frequently Asked Questions
Ready to Transform Your Production Scheduling?
User Solutions has been helping manufacturers optimize their production schedules for over 35 years. One-time license, 5-day implementation.

User Solutions Team
Manufacturing Software Experts
User Solutions has been developing production planning and scheduling software for manufacturers since 1991. Our team combines 35+ years of manufacturing software expertise with deep industry knowledge to help factories optimize their operations.
Share this article
Related Articles
AI in Manufacturing: Practical Applications Beyond the Hype
Explore real-world AI applications in manufacturing: scheduling optimization, quality prediction, predictive maintenance, and demand forecasting for any size shop.

Cloud Manufacturing Software: Benefits, Risks, and When to Stay On-Premise
Evaluate cloud vs on-premise manufacturing software. Security, reliability, cost, and practical guidance for scheduling, ERP, and MES deployment decisions.

Data-Driven Manufacturing: How to Use Production Data for Better Decisions
Learn how to collect, analyze, and act on manufacturing data. KPIs, dashboards, scheduling data, quality analytics, and practical steps for any manufacturer.
